Mobile applications have been one of the most significant revenue generators for many businesses. Their revenue has been close to $693 billion in 2021 and is projected to reach $935 billion in 2023. However, this phenomenal surge comes at a cost of cyberattack threats. That’s why mobile app security is so crucial.
According to the Mobile Security Report 2021, 97% of the organizations have faced mobile-related attacks, with 46% of employees downloading at least one malicious application. This has led to many concerns regarding the businesses and user data security who interact with brands for different purposes. They exchange data with the brands on applications during these interactions, leading to malicious exposure without proper security measures.
That’s why you need reliable security measures to avoid data risks and protect your customers. Check out different best practices that you can use to ensure mobile app security.
- Data Encryptions
- Secure Codes
- User Authentications
- Compliance & Integrity
- Secure APIs
- Security Triggers
- Data Privileges
- Secure Containers
- Protect your Business
1. Data Encryptions

Lots of applications are used by several users across devices and operating systems. So you need to ensure that the data exchanged over the application does not get exposed due to the vulnerability of any OS or device.
One way to do this is by encrypting the data across applications. Encryption is a process of scrambling the data to a point where it becomes unreadable for hackers. There are two ways to encrypt data:
- Symmetric encryption
- Asymmetric encryption
Symmetric encryptions use the same security key for encryption and decryption of data. At the same time, asymmetric encryption has different security keys for encryption and decryption. Another best practice to follow for mobile app security is secure coding.
2. Secure Codes
Every application at its core has an architecture built on several pieces of code. So, when it comes to mobile app security, secure codes can extremely important.
According to a report from IT Pro Portal, 82% of the vulnerabilities appear in the application source code. This means that you need to ensure that the source code is bug-free and there are no vulnerabilities.
Hiring a professional app designer can give you the peace of mind that your mobile app security is airtight. Along with having an expert onboard, mobile application testing is the best way to ensure that the code is secure, and there are no bugs that hackers can exploit.
3. User Authentications
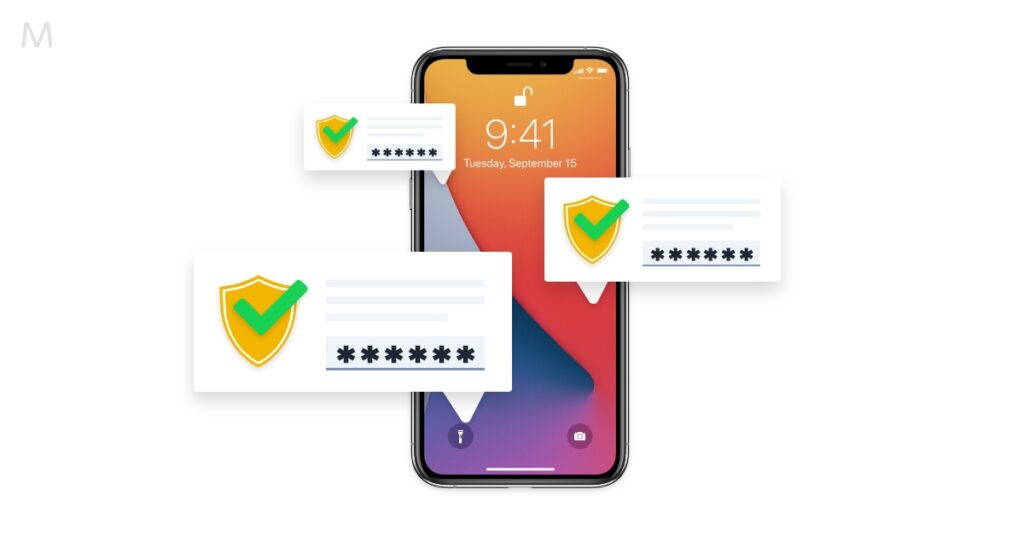
Mobile applications have the highest number of contributions through UGC (user-generated content). UGC can be exposed to cyber attacks without a proper user authentication system in place. Hackers can gain access to vital information of the users leveraging social engineering attacks.
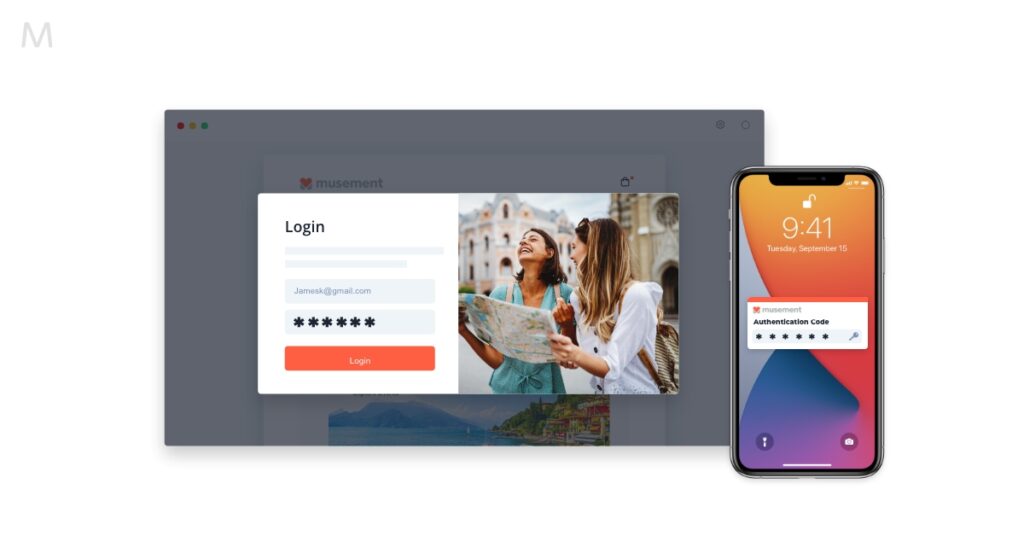
Once they gain access to user accounts, malicious injection becomes easy through UGC. Here, you can employ user authentication processes like multi-factor authentication. However, unlike the traditional authentication process, there is an extra layer of security with one-time passwords, tokens, security keys, or others.
For example, a two-factor authentication process allows users to validate their identity through OTP received on the device. Another essential part of mobile application security is compliance.
4. Compliance & Integrity
When any mobile app is launched, it has to pass certain security parameters and follow requirements. There may be specific security measures to be followed by developers under the app store direction. These measures could be for the download and installation process of an app.
Modern smartphones use app stores to distribute signed apps to users or software that needs code signing. This process ensures that a platform distributes only pre-vetted applications are.
Developers can submit their apps to the store and their identities and the application’s security requirements are validated. If everything corresponds to the operating system’s guidelines, then the application is available for download.
While this may seem daunting, it becomes easy with several coding sign options available in the market. In addition, you can quickly get a cost-effective cheap code signing certificate for your application to ensure compliance and integrity. It proves that the code has not been tampered since its inception and it comes from a genuine publisher.
This certificate helps developers encrypt the information related to their identity, which is further decrypted through a public key offered to users. Another aspect that you need to understand about app security is the APIs or Application Programming Interface.
5. Secure APIs

APIs are essential to integrate third-party services and also improve functionality. It allows heterogeneous systems to interact with each other and facilitate data exchange. However, for better app security, you need secure APIs and do not expose the data exchanged. The best way to ensure API security is to leverage data access authorizations.
6. Security Triggers
You can leverage specific triggers to alert your systems in case of tampering with the application source code. For example, AWS Lambda functions can be leveraged to ensure cloud-native application tampering or malicious injection alerts.
7. Data Privileges
Another way to ensure that your application is not exposed to malicious cyber attacks is by identifying data privileges. Use the approach of least privilege where you provide sensitive data access to limited users. This will ensure that a person without data access and with malicious intent gets access to sensitive information.
8. Secure Containers
One of the most crucial aspects of encryption is security keys. If you are encrypting data for your application, try and avoid the storage of security keys in local data centers.
However, with most organizations leveraging the hybrid cloud approach to store sensitive information in local data centers, you can use secure containers to store these keys. For example, you can leverage advanced security protocols like 256-bit AES encryption with SHA-256 for hashing to ensure security for such keys.
Protect your Business
As smartphone usage increases every day, mobile application security should be high on your priority list. Unfortunately, with deceiving attributes and social engineering practices, hackers are getting efficient at malicious injection attacks.
This means that you need to improve the security measures for data security and stop these hackers from taking control of your applications. We hope that these tips are helpful and we’re always happy to guide you along the way!
Need to chat about your mobile marketing strategy?
More than 10,000 marketers use Maropost to engage with their prospects and customers through emails, SMS, social media and more. We’re here to help you grow your business!
Chat Now